Guest
on 3 March 2016
Tom Barber at Meteorite explains how beneficial Juju Charms has been when migrating customer services from old, tricky servers.
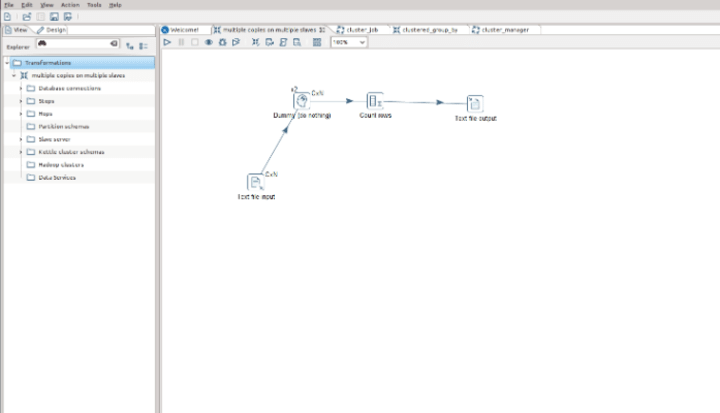
I promised a demo of Juju GUI in my earlier blog and we’ve worked hard on a Pentaho Data Integration charm, so I figured we’d combine the two.
For those of you who don’t know, Juju is an Application Modelling platform developed by Canonical. Pentaho Data Integration is the best Open Source ETL toolkit on the planet. So why not combine the best of both worlds?
At Meteorite we have been migrating customer services from old, tricky to maintain servers to Juju managed clusters and its been an eye opening experience, in a good way! The latest product in our armoury to get the treatment is PDI. Our brief for this is threefold:
Firstly we need an easy way to deploy PDI on a bunch of different servers, in different clouds and maintain it, along with that it needs to provide on demand and scheduled ETL execution.
We also need a way to spin up and configure remote Carte servers for remote execution of ETL jobs and transformations, we would also like self configuring clusters as an added bonus.
Big Data deployment to work with the Big Data charms Juju already provides.
The charm is still under development, don’t expect everything to work yet, some of the functionality hasn’t even got any code written yet, but the charm is available here
Of our brief 1 and 2 are 90% complete, 3 will be done in the not too distant future.
But of course it wouldn’t be cricket if we didn’t give you a quick video demo of how easy it is so spin up a PDI cluster so here we are…
Apologies for the lack of contrast on the terminal, I need to remember to resolve that before the next video, but luckily we’re mostly interested in the GUI and webpages so hopefully it doesn’t impact things too much!
About the author